The Hidden Threat Behind Decentralized Trust
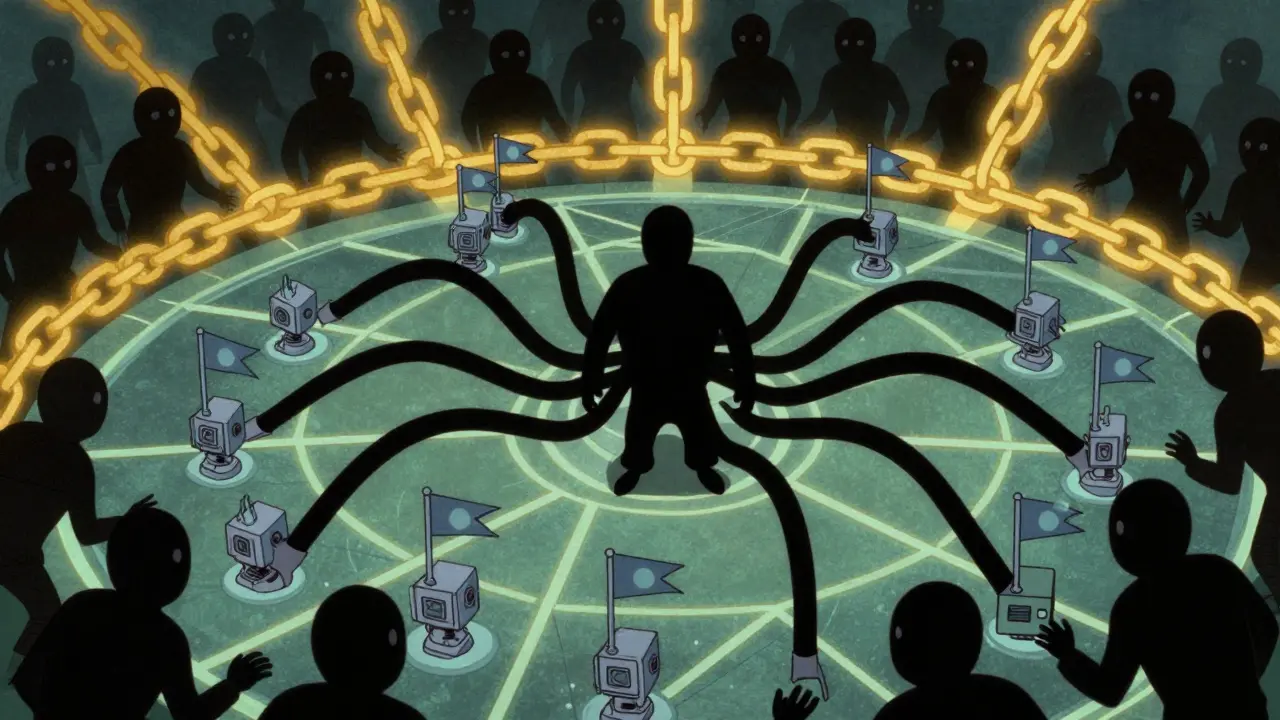
Imagine walking into a town hall meeting where you believe everyone represents a unique voice. Now imagine that one person has sneaked in fifty fake neighbors with costumes and masks to sway the vote. That is essentially what happens during a Sybil Attack a security vulnerability where one malicious actor creates multiple fake identities. Sybil Identity Attack. In the world of digital finance and networking, this isn't just a theoretical nightmare; it is a fundamental risk that keeps engineers awake at night.
When we talk about peer-to-peer networks decentralized systems where participants interact directly without a central authority, P2P Network, we often assume trust is built on code. But code relies on economics and human behavior too. A single attacker controlling hundreds of nodes can distort reality, censor transactions, or even rewrite history in extreme cases. This threat has evolved since its identification in early research, yet it remains relevant today as new protocols launch every week.
Defining the Mechanism of Manipulation
To understand the danger, you have to understand the anatomy of the assault. The term originates from the 1973 book by Flora Rheta Schreiber, which documented a woman with dissociative identity disorder. The concept was later formalized in computer science by Brian Zill at Microsoft Research in 2002. The core idea is simple: a single entity disguises itself as many distinct identities to gain disproportionate power.
In a blockchain a distributed ledger technology secured by cryptography and consensus algorithms, Distributed Ledger Technology, every node validates transactions. If an attacker can register thousands of nodes using botnets or automated scripts, they might convince the network that they represent the majority of honest users. They don't necessarily need to hack the software; they just need to outnumber the legitimate players through sheer volume of fake identities.
This exploits a weak assumption in many decentralized systems: that each connection equals one independent participant. If your reputation system rewards "votes" based purely on connection count, a Sybil attack becomes trivially easy to execute. The attacker generates new IP addresses, spins up virtual machines, and floods the network with requests that look genuine but serve a hidden agenda.
The Ultimate Goal: Taking Control of Consensus
Why go through all this trouble? The objective is usually to achieve what experts call a majority control over network resources. The most dangerous manifestation of this is a 51% attack an event where an entity controls more than half the network's computing power. Once an entity holds more than 50% of the influence-whether that be hash power, stake, or voting nodes-they gain the ability to reorder transactions. They can block specific users from sending money, enable double-spending by validating a transaction twice, or simply reverse payments made to exchanges.
For a privacy-focused blockchain, the stakes are different but equally severe. Attackers can de-anonymize users by observing routing patterns across their controlled nodes. Without robust protections, these vulnerabilities allow bad actors to dismantle the integrity of the ledger, turning a secure financial record into a tool for theft.
| Network Type | Resistance Level | Primary Barrier |
|---|---|---|
| Bitcoin Network | High | Massive Energy Cost |
| Smaller Chains | Low to Medium | Lower Hash Rate/Stake |
| Social Protocol | Very Low | Identity Verification |
Bitcoin and the Economic Wall
You might wonder why we haven't seen this happen to Bitcoin the leading cryptocurrency utilizing Proof of Work consensus. The answer lies in the brutal economics of Proof of Work a consensus mechanism requiring computational effort to validate blocks. In these systems, creating a valid node means solving complex cryptographic puzzles. Doing this en masse requires specialized hardware known as ASIC miners.
Current estimates suggest that executing a successful 51% attack on the Bitcoin network would require controlling over $20 billion worth of mining equipment. Beyond the upfront capital, the electricity bill is astronomical. Mining consumes approximately 150 terawatt-hours of energy per year, comparable to the national grid of a small country. As of our current timeline, this economic barrier makes a Sybil attack financially prohibitive for anyone except perhaps a state-sponsored military entity.
However, this safety is not universal. Every time a new blockchain project launches with fewer miners, the door opens slightly. The market dynamics change quickly, and historical data shows that security gaps are exploited faster than many anticipate.
Vulnerabilities in Smaller Ecosystems
The story changes drastically for smaller networks. We saw a textbook example with Ethereum Classic a legacy blockchain forked from the original Ethereum chain. In 2019, attackers executed a successful 51% attack on this chain. Because the hash rate was lower, the cost to rent enough computing power to dominate the network was manageable for a criminal syndicate. They were able to double-spend significant amounts of cryptocurrency, forcing businesses and exchanges to halt deposits to protect themselves.
This incident highlights a critical truth: decentralization alone is not a shield. You need sufficient economic friction. If your network relies solely on the number of participating nodes without tying that participation to cost or risk, it is vulnerable. Projects relying on pure node count for decisions without validation fall prey to script-kiddies spinning up servers in seconds.

Defense Strategies and Implementation
How do developers protect their systems today? There are four primary categories of defense, though each comes with trade-offs regarding privacy and centralization.
The first is reputation systems. These validate older members as trusted nodes, granting them authority to override suspicious new connections. While effective, this approach risks user privacy, as you need to track history to assign trust scores. Second, identity validation uses central authorities or social proofs where existing trusted nodes vouch for newcomers. Tools like SybilGuard analyze social connectivity graphs to spot abnormal clustering patterns.
The third line of defense involves shifting to Proof of Stake a consensus model securing the network via cryptocurrency holdings rather than computation. Here, influence depends on the amount of coin you lock up. For instance, validators on major networks often need to stake a substantial amount of tokens. This raises the economic cost of attacking significantly because if you attempt an attack and fail, the protocol slashes (confiscates) your staked assets.
Finally, basic security hygiene helps prevent the supply side of the attack. Many fake nodes in the wild come from compromised credentials. Enforcing two-factor authentication (2FA) using apps like Google Authenticator prevents bots from hijacking real accounts to boost their fake node counts. Secure password management ensures individual points of failure don't cascade into network-wide breaches.
Looking Ahead: Emerging Risks
As we move further into 2026, the threat landscape continues to shift. Experts warn that quantum computing could eventually undermine the encryption keys used to verify identity signatures. Current roadmaps suggest practical quantum attacks remain at least a decade away, but researchers are preparing post-quantum cryptographic upgrades just in case. Furthermore, as decentralized finance expands, the value locked in these protocols increases, making the reward for a successful Sybil attack much higher. Security teams are now layering social graph analysis with economic barriers to create multi-stage defense systems. Relying on a single method like PoW or PoS is increasingly viewed as insufficient for long-term viability.
What exactly is a Sybil Attack?
A Sybil Attack is a security vulnerability where a malicious actor creates numerous fake identities or nodes to gain disproportionate influence over a peer-to-peer network. This allows them to manipulate voting, consensus, or routing decisions.
Can Bitcoin suffer from a Sybil Attack?
While theoretically possible, the economic barriers for Bitcoin are incredibly high. Attacking it would require billions of dollars in hardware and massive electricity consumption, making it currently impractical.
How does Proof of Stake prevent these attacks?
Proof of Stake ties network influence to financial stake. To gain control, an attacker must buy and lock up a large percentage of the total token supply. If they act maliciously, they lose their investment due to penalty mechanisms called slashing.
What is the relationship between Sybil Attacks and 51% attacks?
A Sybil Attack is the method of creating fake identities, while a 51% attack is the outcome where one entity gains majority control. Successful Sybil attacks often lead to 51% control of the network resources.
Are there tools to detect fake nodes?
Yes, software like SybilGuard and SybilRank analyzes network connectivity graphs to identify abnormal patterns typical of botnets or fake identities, flagging them for review before they join the main network.

Comments (10)
Ronald Siggy
March 29, 2026 AT 10:32
We see this pattern emerge whenever decentralization meets human greed. Security protocols often fail because they ignore basic incentives. You cannot patch a flawed design with better encryption alone. The network needs to understand the cost of participation deeply. Trustless systems still require trust in the underlying economic model.
Zackary Hogeboom
March 30, 2026 AT 13:47
Proof of work feels outdated but it works for massive chains. Smaller projects struggle with the same logic though. They lack the hash rate to deter bad actors effectively. It makes you wonder if true decentralization is even possible. Many think energy cost is the barrier but bots scale faster.
Tiffany Selchow
March 31, 2026 AT 16:09
The whole thing smells like a pyramid scheme waiting to collapse.
Addy Stearns
April 1, 2026 AT 16:01
Trust is a fragile concept in digital spaces. We build walls around our data with code. But human nature always finds a way through the cracks. Economics drives the behavior of the network participants. When money is involved greed becomes the dominant force. Protocols attempt to mathematically bind these instincts. Yet history proves that incentives are mutable over time. A Sybil attack exploits the gap between identity and reality. We assume a node represents a person or entity uniquely. This assumption fails when replication costs are low enough. Defense mechanisms must evolve alongside the threats. Static solutions crumble under dynamic pressure from adversaries. The future of security lies in multi-layered verification. We cannot rely solely on computational power for safety. True resilience requires a blend of social and economic constraints. Ignoring this complexity invites disaster upon the system.
Raymond K
April 2, 2026 AT 15:02
I tottaly agrree with the support shown here. Becuase recieving trust is hard in teh blockchain world. Cryptocurrenccy miners need more protection form bots. We shoulld invest in better idendity checks. It is sad how easy it gets hacked sometime. Hope we can fix thie soon. Teh economy is what matters mosrt.
Jamie Riddell
April 3, 2026 AT 04:34
sorry but small chains are definitely more vunerable to these kinds of attacks. i hope developers prioritize security over speed now. keeping the ledger safe is paramount for everyone. good read overall
Wade Berlin
April 5, 2026 AT 04:21
It is hilarious how people think new chains are safer than Bitcoin. They launch with half the code and zero audit trails. Then they cry when their coins get stolen again. Security theater is not actual security. Stop pretending decentralization fixes stupidity.
Liam Robertson
April 6, 2026 AT 18:00
I do think we need to look at social proof too. Just having expensive hardware is not enough sometimes. People verify nodes differently in real life online groups. We can use those signals for tech networks. It makes sense to combine methods.
Elizabeth Akers
April 8, 2026 AT 06:55
quantum computing changes the game entirely in my view current keys will be obsolete fairly quickly we need to upgrade protocols before then happens many devs ignore this looming threat unfortunately
Lisa Miller
April 8, 2026 AT 09:28
Love seeing such detailed breakdowns on security risks. We all need to stay aware of these vulnerabilities in our wallets. Protecting your own assets starts with knowledge like this. Keep up the great work on educating us all!